Bytom System Review and Rating (SVET)
Bytom is one of those projects which launch marginally preceded 2017 crypto rush. Its founders were obviously inspired by the rise of the Ethereum and tried to come out with a better (as they thought) alternative which is supposed to combine UTXOs with smart contracts.
Initially, when I read Bytom whitepaper at the fall 2017, I was not impressed by it due to its absence of technical details. Besides, its original version and Bytom website were both in Chinese and only the dubious quality translation of the former was made available for me at that moment.
That’s how, although authors idea to create an interoperable chain allowing exchange of wide varieties of digital assets had resonated with my own vision, I have been staying away from this project for quite a while. Nonetheless, since then Bytom had been added to my watch list although its performance to date was wanting.
However, just recently Bytom has launched its test net and I’ve decide to revisit this project again. Hence my recent review and rating whixh are based on the latest version of the Bytom technical white paper available on their site and dubbed “Bytom An Interoperation Protocol for Diversified Byte Assets”.
Overall, it produces an impression of a slight decadence, both on the system architect and implementation levels. Author choice to introduce into their protocol the, so-called, ‘control contracts’, allowing roll-backs, although, explainable from the point of view of projects locality, at the same time, seriously undermines platform security creating a large attack surface for a wide variety (individual and group) malicious actors. Security is ‘c+’..
I might relate this paradox to the regional factor but, for example, while Bytom has only about two-and-a-halve thousand members in its ‘Bytom Official English Group’ group, its ‘Chinese Group’ is even smaller — under two thousands.
Extract: “Bytom consists of three layers: data transaction and transmission layer, contract layer and asset interaction layer.”
Extract: “The contract layer use genesis contract and control contracts for asset issuance and management, supporting scalable BUTXO of UTXO model at the bottom layer, optimizing EVM and using introspection mechanism to prevent deadlock in Turing complete.”
Additionally, combining UTXO with smart contracts had been a relatively popular theme, which I’d met in at least a couple other whitepapers during a period of 2018–2019.
As far as I know neither of such ‘hybrid’ solutions went live (not to mention were adapted by sufficiently large number of users). Besides, the practical viability of those types of protocols is questionable and their vulnerability might be very high due to their experimental nature. However, I’m ready to give authors the benefit of a doubt and assign ‘b-’ instead of ‘c’ to the ‘Engineering’ side of the rating.
Now to the Bytom’s throughput and scalability. As authors pointed out themselves: “ … performance is sacrificed to meet the demands of decentralization and security (comprehensive integrity) as described in the Impossible Triangle”. Although I have to assign ‘c+’ to ‘Velocity’ sub-rating it doesn’t prevent me from expressing my regards to author’s voluntary disclosure of their protocols weaknesses and vulnerabilities.
Assessing Bytom’s ‘Transparency’ (decentralization) presents an issue to me because from the one side, as I have already mentioned, I am not appreciative of the control contracts, but, from the other, I can see the purported necessity of their existence given that maintaining a multitude of assets requires some types of consolidating mechanism. However, one additional protocol’s feature settles this matter for me. I’m talking about Bytom declared adaption of the AI ASIC chips.
Extract: ‘Bytom proposes a consensus algorithm that is friendly to AI ASIC chips so that the hashing power can be applied to the AI hardware acceleration service, thus solving the hardware consumption problem of PoW miners.’
Of course, I do realize that it might not have a slightest effect on pool miners’ ability to centralized hash-power (AI or not) because, most users might simply be too lazy to resist their convenience. However, the fact that this attempt for decentralization was entertained by the authors means a lot from my point of view. Hence, ‘Transparency’ is ‘a-’.
Result for ‘System’ (Security — Velocity — Engineering — Transparency): c+/c+/b-/a-
For the original version of this article, please, refer to: http://svetrating.com/rating_text/37/system/
Link (Bytom WhitePaper): https://bytom.io/wp-content/themes/freddo/book/BytomWhitePaperV1.0_En.pdf
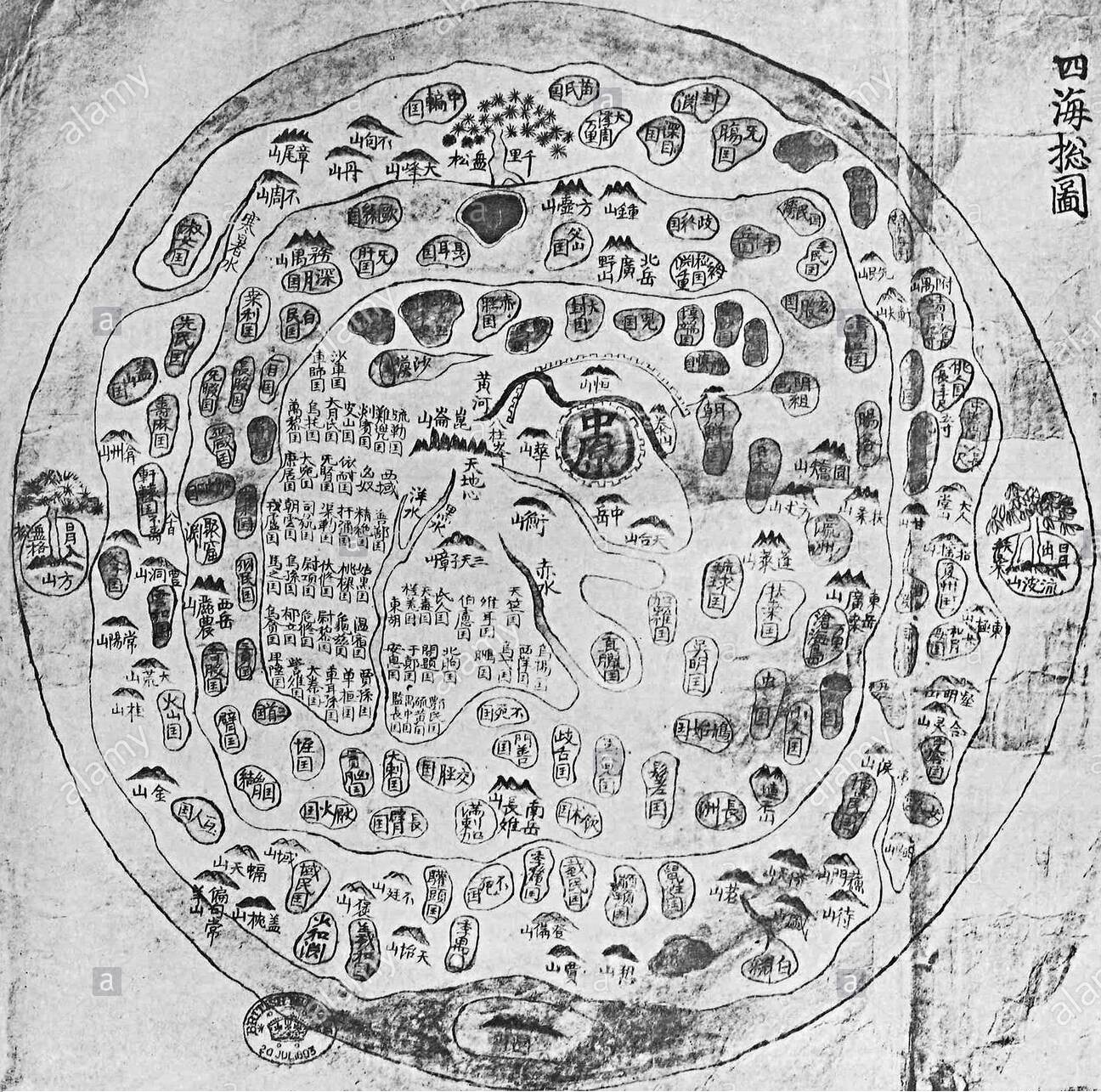
Image: Chonhado (map of all under heaven), 17th century.
What Is SVET Rating?
Hidden Fundamentals' Leading Indicator
- Security (safety): for defenders (ISFJ- The Protector: Warm-hearted and dedicated, they are always ready to protect the people they care about.);
- Velocity (scalability): for megalomaniacs (ENTJ- The Commander: Outspoken and confident, they are great at making plans and organizing projects.);
- Engineering (design): for geeks (INTJ- The Architect: High logical, they are both very creative and analytical.);
- Transparency (decentralization): for crypto punks (ISTP- The Crafter: Highly independent, they enjoy new experiences that provide first-hand learning.);
- Singularity (uniqueness): for Individualists (ISFP- The Artist: Easy-going and flexible, they tend to be reserved and artistic.);
- Volume (market): for Globalists (ESFP- The Performer: Outgoing and spontaneous, they enjoy taking center stage.);
- Empathy (enthusiasm): for Tribes (ESTP- The Persuader: Out-going and dramatic, they enjoy spending time with others and focusing on the here-and-now.);
- TimeLine (road-map): for Visionaries (INFP- The Mediator: Idealistic with high values, they strive to make the world a better place.);
- Solution (business): for Dealmakers (ESTJ- The Director: Assertive and rule-oriented, they have high principles and a tendency to take charge.);
- Validity (legality): for Lawyers (ISTJ- The Inspector: Reserved and practical, they tend to be loyal, orderly, and traditional.);
- Equity (finance): For Venture Capitalists (INFJ- The Advocate: Creative and analytical, they are considered one of the rarest types.);
- Team: for Friends (ESFJ- The Caregiver: Soft-hearted and outgoing, they tend to believe the best about other people.);
- Sustainability (stability): for Sages (INTP- The Thinker: Quiet and introverted, they are known for having a rich inner world.);
- Value (venture): for Adventurers (ENTP- The Debater: Highly inventive, they love being surrounded by ideas and tend to start many projects (but may struggle to finish them).);
- Engagement (usability): for Pragmatics (ENFJ- The Giver: Loyal and sensitive, they are known for being understanding and generous.);
- Transactions (speed): for Travelers (ENFP- The Champion: Charismatic and energetic, they enjoy situations where they can put their creativity to work.).
Here might be your Review.
Why Shall You Use the SVET Platform?
Community Members
Start building your wealth with only USD 100.
Founders
Gain a competitive edge by leveraging experts opinion.
Investors
Get a first-mover advantage.
